![]()
Black Friday – there’s Malware in the specials!
Although we don’t celebrate Thanksgiving here in Australia, it doesn’t mean that we don’t get to enjoy the benefits of the Black Friday and Cyber Monday specials; with 2018 being one of the more lucrative years for these occasions. However, if you are going to partake in Black Friday/Cyber Monday shopping in future, please be aware that scammers and other malicious actors like to take advantage of these days too.
As Wired reports, the typical retail scams all apply – phishing emails trying to sell cheap Gucci sunglasses, fake websites trying to steal your credit card details and attackers planting Malware and cryptojacking modules where they think consumers might click. They also say that “malicious websites, apps, emails, texts and other lures try to motivate victims to take action. They might offer a time-limited deal, or a low price that's hard to turn down to try to get targets to act before they think. That's partly why they're so dangerous around Black Friday; retailers use the same tactics to promote their sales.” With this said, following your intuition might be your best form of defence – “you're never, ever going to see the latest iPhone model for 70 percent off.” RiskIQ has found that 5.5% of the apps mentioning Black Friday or Cyber Monday “were malicious apps that contain credit card number skimmers, adware, Malware, or even mobile ransomware. Scams popped up more frequently on third-party app stores than Google Play and Apple's App Store, but offending apps showed up everywhere.”
The long and the short of it? As we approach any major holiday, it’s probably best to remember this – if a deal seems too good to be true, it probably is.
Amazon leaks customer data in Black Friday
Following on from the above, last year, Forbes reported that Amazon had “inadvertently disclosed” customer names and email addresses due to a “technical error." Amazon reached out to impacted customers with the following email:
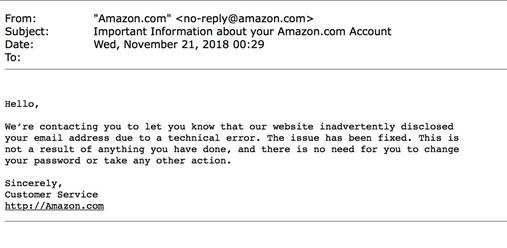 Customers were naturally pretty annoyed at the lack of information provided by Amazon, including to whom the information was inadvertently disclosed. Amazon has not made any details of the “technical error” public so far.
Customers were naturally pretty annoyed at the lack of information provided by Amazon, including to whom the information was inadvertently disclosed. Amazon has not made any details of the “technical error” public so far.
Millions of 2FA codes and reset links exposed
Ars Technica is reporting that a database belonging to Vovox – providers of an SMS gateway to businesses that want to automate sending of information for password resets and other account management SMSs – has been exposed on the internet for all to see. More than 26 million SMS messages – many containing one-time passcodes, password reset links, and plain-text passwords – were discovered by a security researcher using Shodan to search for publicly accessible databases. The database also provided a portal displaying near real-time updates of 2FA codes and password reset links being sent to users, making it possible for an attacker to obtain the information necessary to be able to access a victim’s account protected by a password and 2FA code.
Due to the vulnerable nature of SMS-based 2FA, the ASD/ACSC’s Essential Eight allows only the following factors to achieve Maturity Level Three – U2F security keys, physical OTP tokens, biometrics and/or smartcards.
Contact Us today to find out how Thomas Duryea Logicalis can support you with your organisation's security concerns and posture.



